The ideal alternative to Citrix and Microsoft RDS for remote desktop access and Windows application delivery. Web-enable your legacy apps using Seamless RDP. Problem you are facing now. Retail Manager and MYOB RDP can improve the performance of your MYOB Premier and Accounting, Retail Manager, QuickBooks and
Read more →1. Turn off Password Protected Sharing from the Control Panel First, you can try to turn off the Password Protected Sharing from the Control Panel, and see if it works properly for you. If you already tried this method, go straight to the next solution. To do so, you
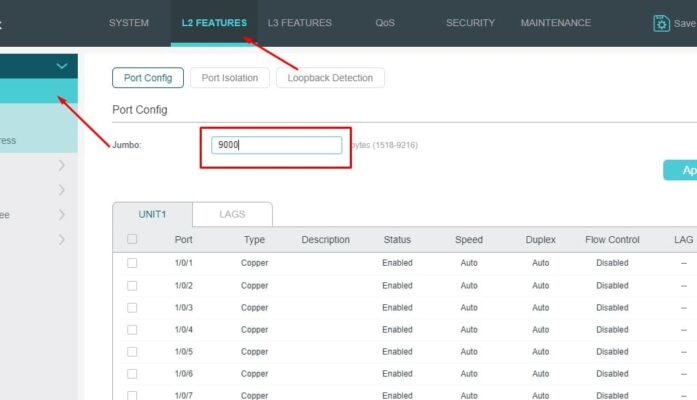
Read more →Jumbo Have to enable to 9000 bytes 2. If you have Video multicast traffic source. you need to separate a VLAN for video else the switch will jam due to multicast traffic. Let say we create vlan 2 is video, vlan 3 is voice. please refer
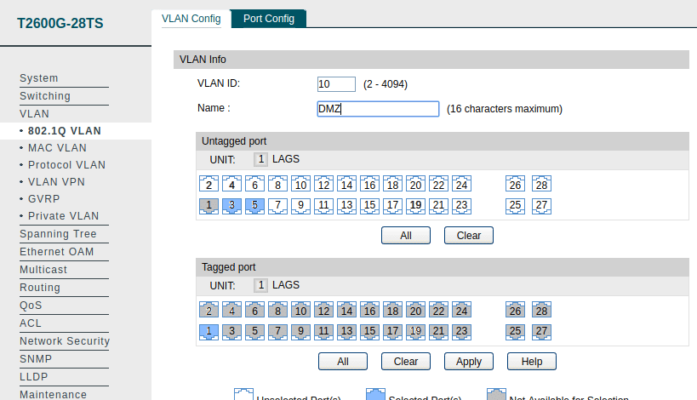
Read more →VLAN (Virtual Local Area Network) is a technology that can solve broadcasting issues. A LAN can be divided into several VLANs logically, and only the hosts in a same VLAN can communicate with each other. Here is a configuration example for 802.1Q VLAN. sample tplink config on
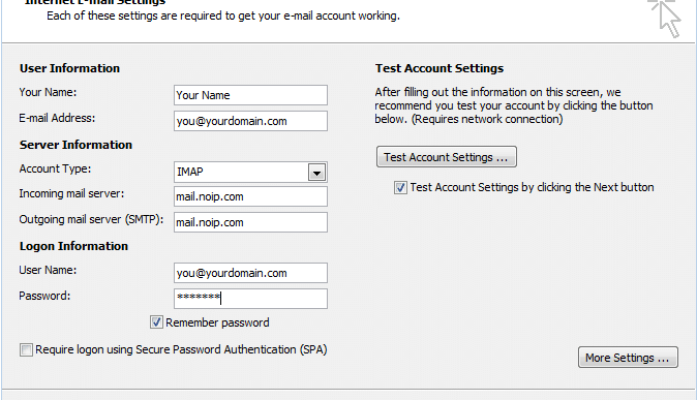
Read more →In order to add your email account to Outlook, Outlook on the web, Outlook.com, or the Mail and Calendar apps for Windows 10, you’ll need several pieces of information including the type of account, the incoming and outgoing server names, and the SSL and port settings. Email
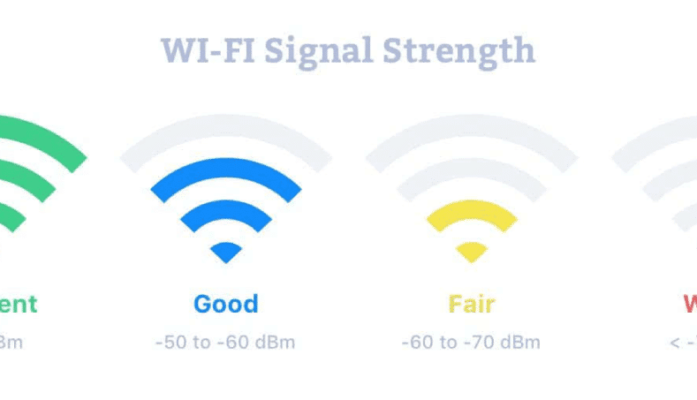
Read more →What is RSSI and what does it mean for a WiFi network? RSSI, or “Received Signal Strength Indicator,” is a measurement of how well your device can hear a signal from an access point or router. It’s a value that is useful for determining if you have
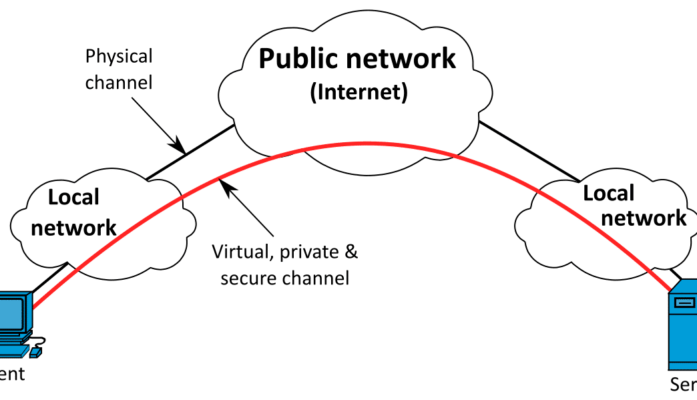
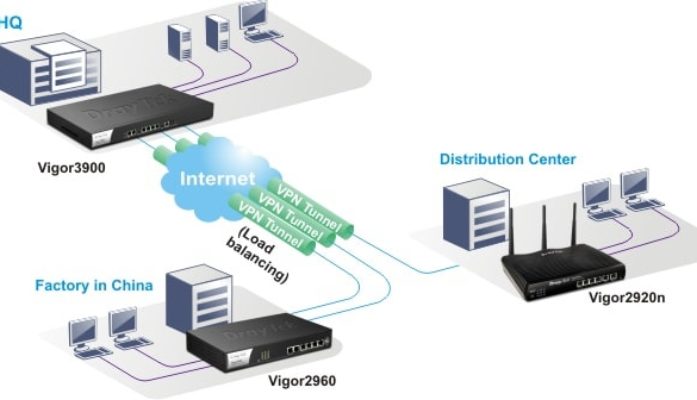
Read more →model: Vigor 2925 and Vigor 2926 HQ: (dynamic ip address) a) put in the peer id (both must same on HQ and Branch) b) IKE pre-shared key (both must same on HQ and Branch) Step: 1. go to vpn and remote access -> lan to lan 2. create
Read more →Maxis Business fiber will having issue to setup on other router if the user want to use their phone (free line). they cannot attach to the TM modem as per this equipment is not own by maxis. If you want to use the phone line from maxis
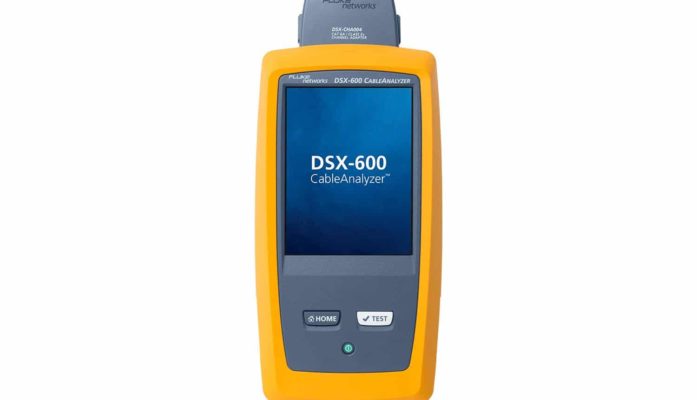
Read more →Essential certification of copper, twisted pair structured cabling from Cat 3 / Class C through Cat 6A / Class EA The DSX-600 from Fluke Networks provides essential Cat 6A and Class EA Copper Certification featuring ten second test times and advanced user interface. Manage jobs and testers from
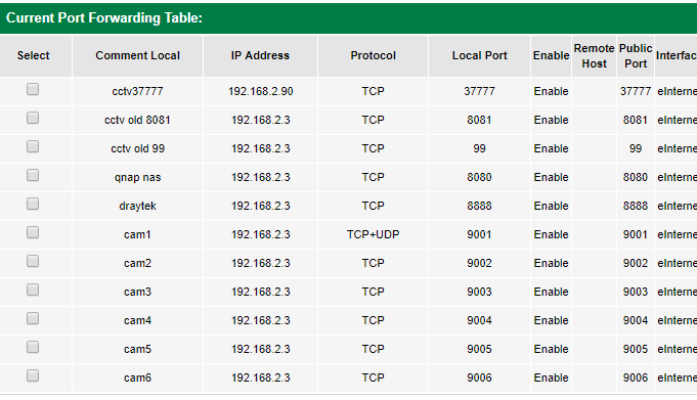
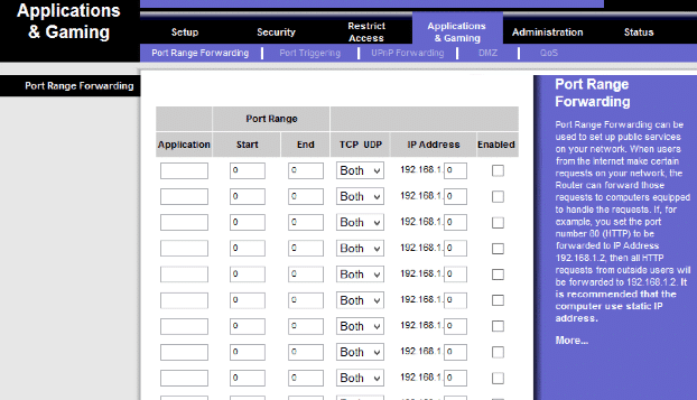
Read more →On router 2, you need to open the port assign to the wan port of router 1. for example 192.168.22.5 cctv use 37777 tcp on router 1, you need to open the port assign to the DVR. for example 192.168.8.19 cctv use 37777 tcp.
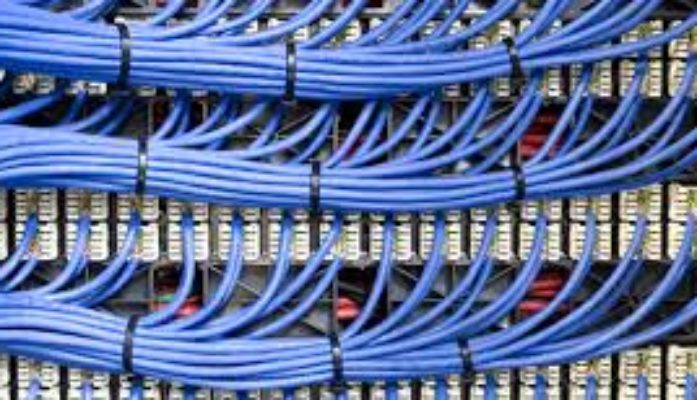
Read more →The conveyance media you choose for your structured cabling implementation is determined by many factors, the most important of which are your current bandwidth needs, your network environment, your expected future bandwidth requirements and your budget. This article will address each of these primary concerns in an
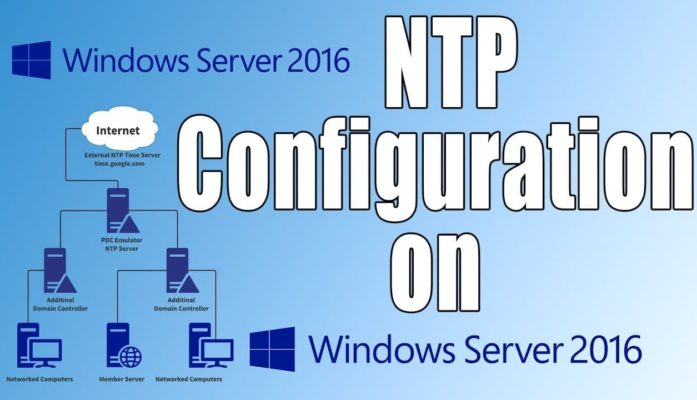
Read more →The quickest way to synchronise your clock with the domain time, open a command prompt window and type: NET TIME /DOMAIN To force a computer to synchronize its time with a specific computer, send the following command: NET TIME \\<MACHINENAME> /SET /Y -or- NET TIME \\<IP Address>
Read more →One of the most common root causes for having slow and unstable wireless network connections is interference. Many things interfere with a wireless network: everything from walls to the microwaves you use in the kitchen to other wireless networks. That’s why I decided to learn more on
Read more →Web Content Filtering DrayTek’s Web Content Filtering (WCF) facilities enable you to protect your network and your users from web content according to your preferences. There are many reasons for doing this, for example: Reason to Block Example Unsuitable Adult material for children Undesirable Time wasting sites
Read more →Replacing Unifi Maxis Router with Fortinet Fortigate 40c with Unifi router/ maxis router 1. For fortigate 40c, the GUI configuration are limited, so have to set it using CLI. 2. Type following command to create sub-interface config system interface edit unifi set type vlan set vlanid
Read more →The Hidden Hero of the IT cabling Cabling is one of the most important elements within any IT network and is one of the biggest IT investments that companies make. Selecting the right cabling system can have a tangible impact on a range of issues, including network
Read more →