Google is discontinuing its G Suite legacy free edition from July 1 and have reminded users to upgrade to Google Workspace if they wish to maintain their services and accounts. According to website 9to5google, the company’s recent email reminders to existing G Suite legacy users stated that they have
Read more →If You Own A QNAP NAS That May Have Be Exposed to The Hack, Check It Now and Block All External Access Until You Are Sure the Firmware and Apps Have Been Updated. I have log the case to QNAP Support and below is their reply: PLEASE
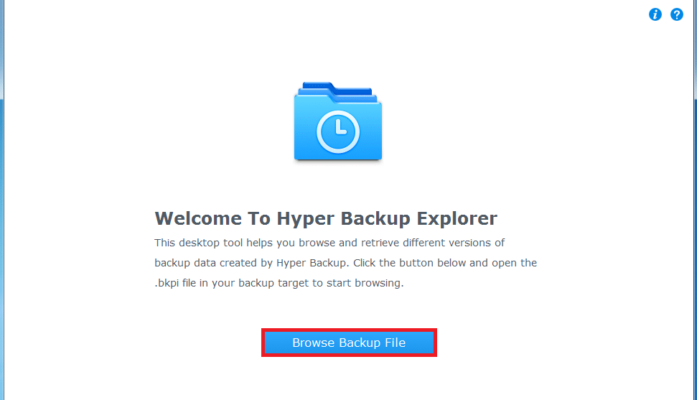
Read more →Hyper Backup Explorer is a compact desktop tool that runs on client computers (Windows, Mac, and Linux). It is designed for feature evaluation, access to multi-version backups, and emergency data retrieval. This desktop tool helps you browse and retrieve backup files stored in proprietary repositories created by
Read more →Make a recovery plan against encryption-based locker viruses(Ransomware) Ransomware is a rising threat against both business and home users that targets computers and network-based devices. A simple yet effective method of mitigating the threat of ransomware is to ensure that you always have up-to-date, remotely-stored backups. QNAP
Read more →The nefarious ransomware business model has turned out to be a lucrative industry for criminals. Over the years its ill repute has made law enforcement team up with international agencies to identify and bring down scam operators. Most of the ransomware attacks that have taken place in
Read more →In today’s time and age, one has to take safety and security as some of their top priorities. You know how whistleblower Edward Snowden revealed that the National Security Agency (NSA) accesses the central servers of major companies like Microsoft, Google, Yahoo, AOL, Skype, Apple, Facebook, YouTube,
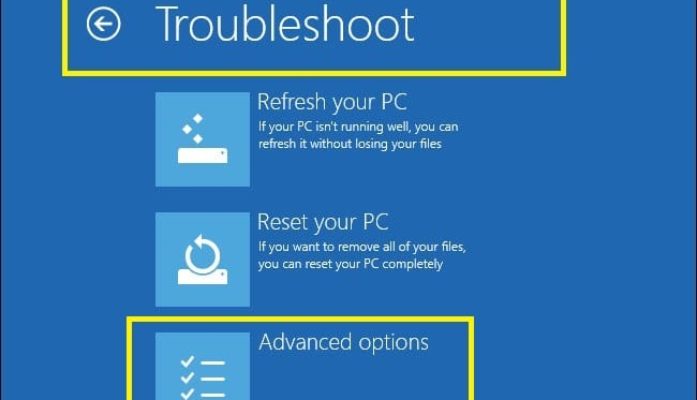
Read more →Below is some guideline of the shortcut key to perform the factory reset for following brand of PC/Laptop Acer – Alt + F10 Asus – F9 Dell/Alienware – F8 HP – F11 Lenovo – F11 MSI – F3 Samsung – F4 Sony – F10
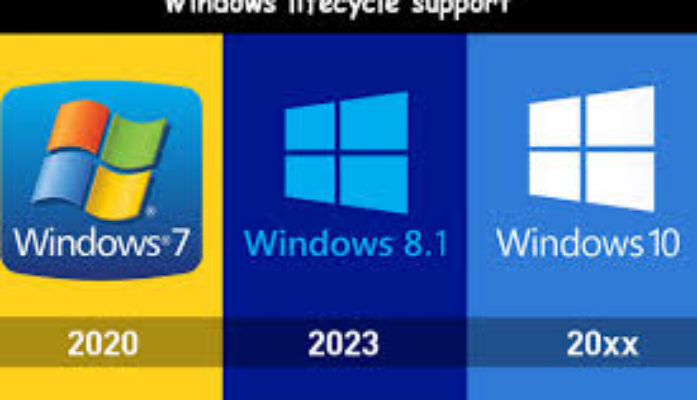
Read more →Every Windows product has a lifecycle. The lifecycle begins when a product is released and ends when it’s no longer supported. Knowing key dates in this lifecycle helps you make informed decisions about when to upgrade or make other changes to your software. End of support End
Read more →Taipei, Taiwan, December 1, 2015 – QNAP® Systems, Inc. today announced the world’s first and only QTS-Android Combo NAS – TAS-168 and TAS-268, which support QTS & Android™ dual systems. Both systems share the same storage database, allowing users to simultaneously access media files and documents from QTS
Read more →Are you a Windows 8 user? Still using Windows 7? Either way, you’ll love Windows 10. Over the six years since Windows 7 was released, Microsoft has made its PC operating system far more intuitive and powerful by packing it with tablet- and smartphone-like features. Windows 10
Read more →With the 4G telecommunications systems now starting to be deployed, eyes are looking towards the development of 5th generation or 5G technology and services. Although the deployment of any cellular system takes many years, development of the 5G technology systems is being investigated. The new 5G technologies
Read more →